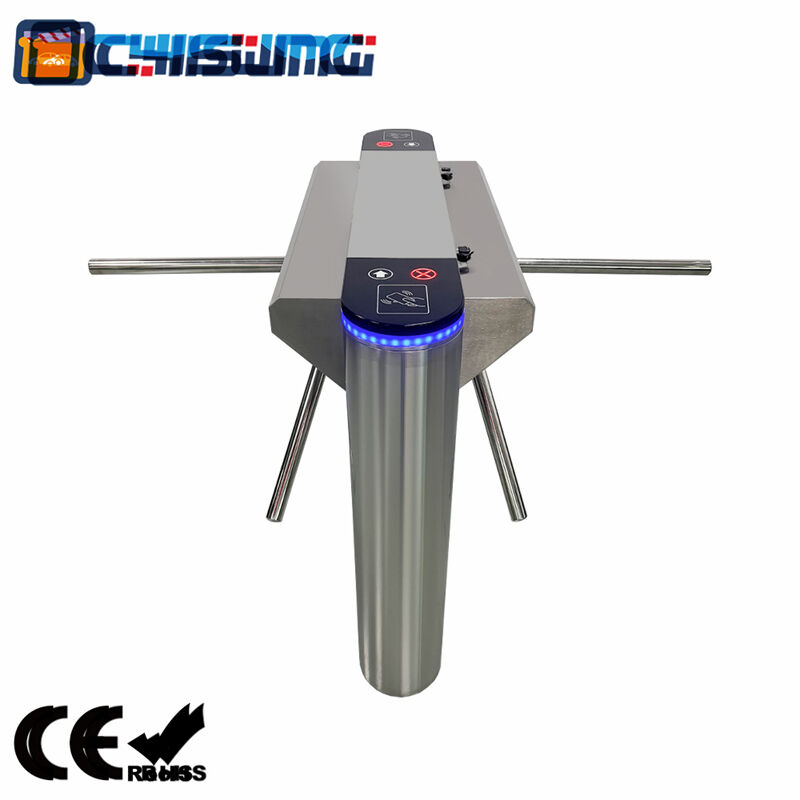
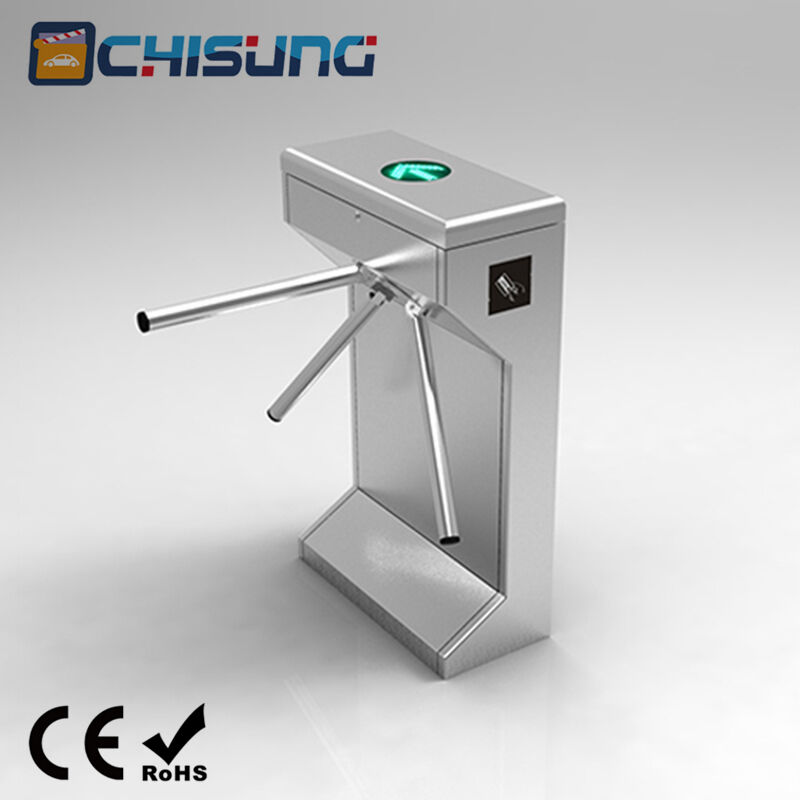
glass turnstile gate
The glass turnstile gate represents a sophisticated access control solution that combines modern design aesthetics with advanced security technology. This elegant barrier system utilizes transparent tempered glass panels mounted on a robust mechanical framework, creating an effective pedestrian control mechanism for various commercial and institutional environments. The glass turnstile gate operates through precise sensor technology, including infrared detection systems, RFID readers, and biometric scanners, ensuring authorized personnel can pass through while preventing unauthorized access. The transparent glass construction maintains visual connectivity between spaces while establishing clear physical boundaries, making it ideal for locations requiring both security and openness. These systems typically feature programmable logic controllers that manage entry and exit protocols, allowing administrators to customize access permissions based on time schedules, user credentials, or specific security requirements. The glass turnstile gate incorporates fail-safe mechanisms that automatically unlock during emergencies, ensuring compliance with fire safety regulations and building codes. Installation versatility allows these systems to integrate seamlessly with existing security infrastructure, including surveillance cameras, alarm systems, and centralized access control platforms. The modular design accommodates various architectural requirements, with options for different glass heights, widths, and finishing materials to match interior design schemes. Maintenance requirements remain minimal due to the durable construction materials and self-diagnostic capabilities that monitor system performance and alert facility managers to potential issues. The glass turnstile gate delivers reliable operation in high-traffic environments, processing thousands of daily passages while maintaining consistent security standards. Advanced models incorporate artificial intelligence algorithms that analyze pedestrian flow patterns, optimizing throughput efficiency during peak usage periods. These intelligent systems can distinguish between authorized users, visitors, and potential security threats, automatically adjusting response protocols accordingly.